Healthcare systems are frequent targets for ransomware and phishing. Protecting sensitive patient information requires layered security and proactive monitoring.
If EHR or scheduling systems become unavailable, care delivery can slow or stop. Reliable infrastructure and rapid support are critical.
Providers and staff often require remote access to systems and secure messaging capabilities without exposing patient data to unnecessary risk.
As staff roles change, managing permissions and securing clinical devices is essential to reduce risk and maintain operational continuity.
 In the Office In the Office |  Providers & Remote Access Providers & Remote Access |  Across the Practice Across the Practice |
|---|---|---|
| Stable and secure network infrastructure | Rapid troubleshooting to minimize disruption | Ransomware prevention and proactive monitoring |
| EHR and practice management tool administration | Secure remote access to clinical systems | Structured onboarding and offboarding |
| Protected email and communication tools | Device management for laptops and tablets | Security best-practice guidance |
| Backup and recovery for critical systems | Multi-factor authentication and identity control | Strategic IT planning aligned with operational goals |
We manage the configuration, access, and security settings that keep your business tools stable and protected.
We assist with:
Our healthcare-focused support is built on three core service areas that ensure reliable support, strong security, and long-term technology alignment.
Proactive support and monitoring that keeps systems stable and responsive.
Layered protection to reduce downtime and financial risk.
Long-term technology planning aligned with project growth.
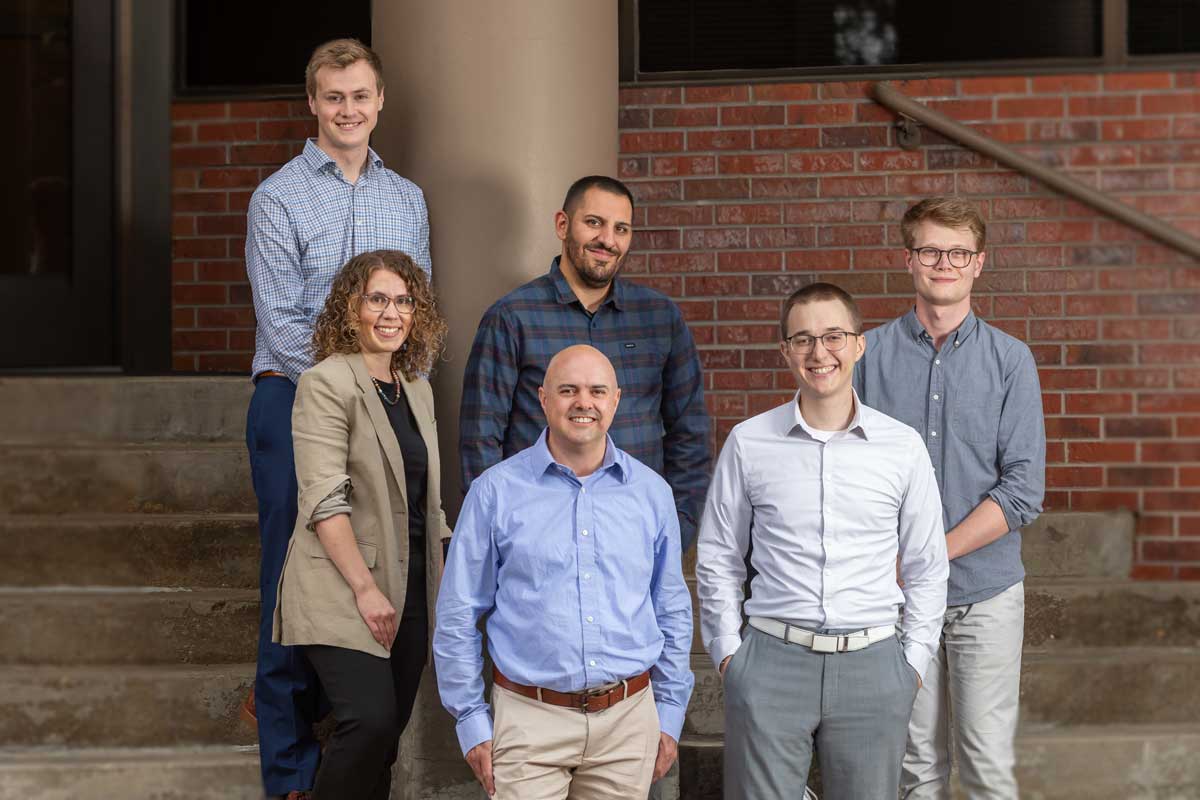
Your IT provider should strengthen your operations, not complicate them. At Onset Solutions, we combine Denver-based expertise, proactive strategy, and personalized service to deliver dependable support that reduces risk and supports long-term success.
Healthcare technology requires careful planning, strong safeguards, and responsive support. Let’s schedule a conversation to understand your practice’s systems, workflows, and security priorities.
We implement layered security measures to protect your environment including endpoint protection, multi-factor authentication, encryption, and continuous monitoring. Our goal is to reduce risk while maintaining secure access for providers and staff.
We do not provide legal or formal compliance certification services. However, we support healthcare organizations by implementing security best practices and technical safeguards that align with healthcare security expectations.
Healthcare organizations are frequent targets for ransomware, phishing, and credential-based attacks. Because patient data is highly valuable, proactive monitoring and structured access controls are critical.
Yes. We help secure remote access to clinical systems through encrypted connections, multi-factor authentication, and managed devices to reduce exposure while maintaining accessibility.
We follow a structured process to provision accounts, configure devices, and assign appropriate permissions. When staff leave or roles change, we promptly remove access to reduce risk.
Yes. While many issues are resolved remotely, we provide on-site support across the Denver metro area for infrastructure upgrades, device deployments, and network installations.
Costs vary based on the size of your practice, number of users, systems in place, and security requirements. We provide tailored recommendations after a brief consultation to ensure pricing aligns with your operational needs. Contact us below to start the conversation.
Your systems should enable care delivery, not create risk or disruption. Let’s review your current environment and identify practical ways to strengthen security and reliability.

Stay ahead of evolving tech challenges with insights tailored to the healthcare industry. From cybersecurity best practices to strategic IT planning and compliance tips, our blog delivers practical advice to help you reduce IT risk, stay secure, and grow with confidence.
Want insights delivered straight to your inbox? Subscribe to our blog to stay updated on the latest IT strategies, security tips, and technology trends for Colorado businesses.